Wazuh v2.0.1 released!


We are happy to announce that Wazuh v2.0.1 has just been released!
As many of you already know, we released Wazuh v2.0 back in April this year. It included the integration of our forked version of OSSEC with OpenSCAP and Elastic Stack 5. In addition, we improved some core capabilities for infrastructure security monitoring, and developed a new WUI in the form of a Kibana app. You can learn more here: Wazuh v2.0 released.
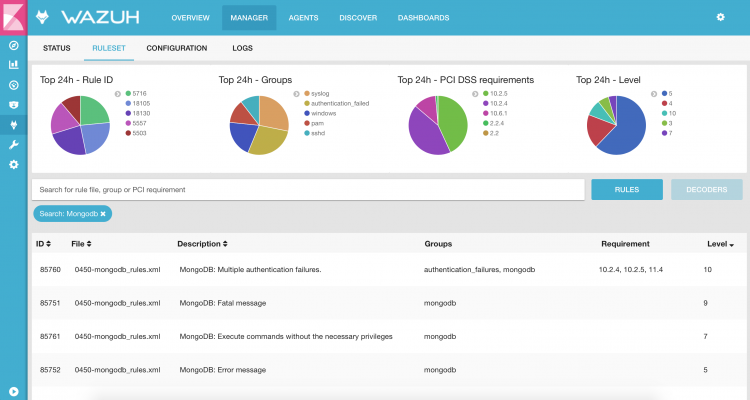
This new released, Wazuh v2.0.1, come with additional rules and decoders as well as other interesting changes in the core code and the API.
Here are the highlights of the new release:
We have added new rules and decoders to analyze log messages generated by the following applications:
Additionally, the ruleset can be updated using our script update_ruleset.py that now accepts a custom download URL.
Here are some interesting changes:
To see the complete list of additions, changes and fixes included in this new release, check the changelog.
Also, here are other useful links:
We would also like to thank our developers, contributors, and users. We are looking forward to your feedback, so please don’t hesitate to post on our mailing list if you have any questions about Wazuh v2.0.1 You can also join our #community Slack channel.