Lately, not only the tech and related communities, but also pretty much everyone else has heard of GDPR, the new standards for security compliance.
GDPR (General Data Protection Regulation) has been drawn up to make privacy legislation consistent throughout Europe, with its main focus on providing data protection for all citizens in the European Union.
To this end, it seeks to increase the privacy of such data and to reform the way in which EU organizations approach data privacy.
As we can see, this regulation has significant impact in today’s world as personal information is vital for many companies and the requirements for compliance with GDPR must be met or severe economic sanctions will be applied.
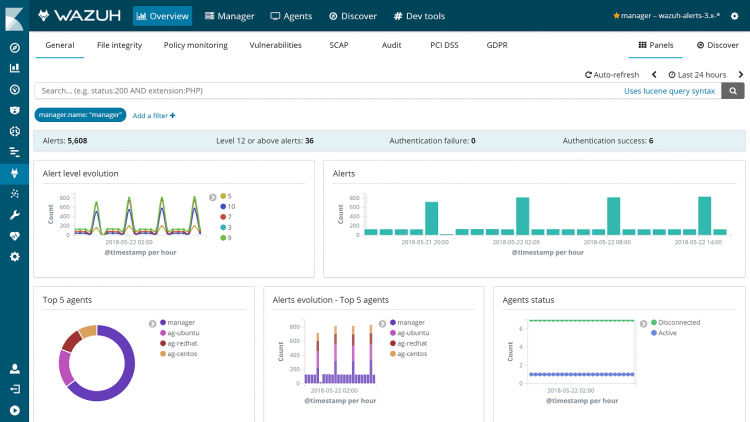
At Wazuh, we have adapted our software in the best possible way to support GDPR compliance, with the addition of:
- A new tagging of our set of rules adding information about GDPR technical requirements.
- A new tab regarding GDPR in the Wazuh app for Kibana that will give visual insight into compliance.
Using Wazuh file integrity monitoring and intrusion detection tools will allow processing and control of personal information as well as protection by means of threats detection, facilitating the fulfillment of security policies.
According to section 5.1.f of the GDPR,
Principles relating to processing of personal data
Personal data shall be: processed in a manner that ensures appropriate security of the personal data, including protection against unauthorised or unlawful processing and against accidental loss, destruction or damage, using appropriate technical or organisational measures (‘integrity and confidentiality’).
the storage and all processing of personal data must be properly processed and protected.
Let’s take a closer look with an use case.
A company stores data belonging to a certain subject:
root@agent:/home/agent/personal_records# cat subject_data.txt First name: James Surname: Harden Marital Status: Married Date of birth: 11/24/1989 Place of birth: Granada, España Social security number: 1111 2222 3333 4444
We will configure the Wazuh agent so the previous file is monitored by the file integrity monitoring tool:
root@agente:~# vim /var/ossec/etc/ossec.conf <!-- File integrity monitoring --> /home/agent/personal_data
Then a user accesses and alters the file contents:
careless_user@agent:/home/agent/personal_datacat subject_data.txt First name: James Surname: Harden Marital Status: Married Date of birth: 11/24/1989 Place of birth: Granada, España Social security number: 1111 2222 3333 4455
The Wazuh manager receives the event for this change and generates the corresponding alert:
{
"timestamp":"2018-05-25T15:41:57+0200",
"rule":{
"level":7,
"description":"Integrity checksum changed.",
"id":"550",
"firedtimes":1,
"mail":false,
"groups":[
"ossec",
"syscheck”
],
"gpg13":[
"4.11"
],
"gdpr":[
"II_5.1.f"
]
},
"syscheck":{
"path":"/home/agent/personal_data/subject_data.txt",
"size_after":"162",
"perm_after":"100777",
"uid_after":"0",
"gid_after":"0",
"md5_before":"991de94df73c387477b2d6ec1bd427e1",
"md5_after":"ca9bc297e343dc6864b1d35f990fdacd",
"sha1_before":"1c085bf5e1960915b23131c2e6c6ea28a41d164d",
"sha1_after":"fbc5cf512d8d6c382b146bc854c08fad76624daf",
"uname_after":"root",
"gname_after":"root",
"mtime_before":"2018-05-18T15:33:26",
"mtime_after":"2018-05-18T15:41:56",
"inode_after":438395,
"diff":"6c6\n< Social security number: 1111 2222 3333 4444 \n---\n> Social security number: 1111 2222 3333 4455 \n",
"event":"modified"
},
}
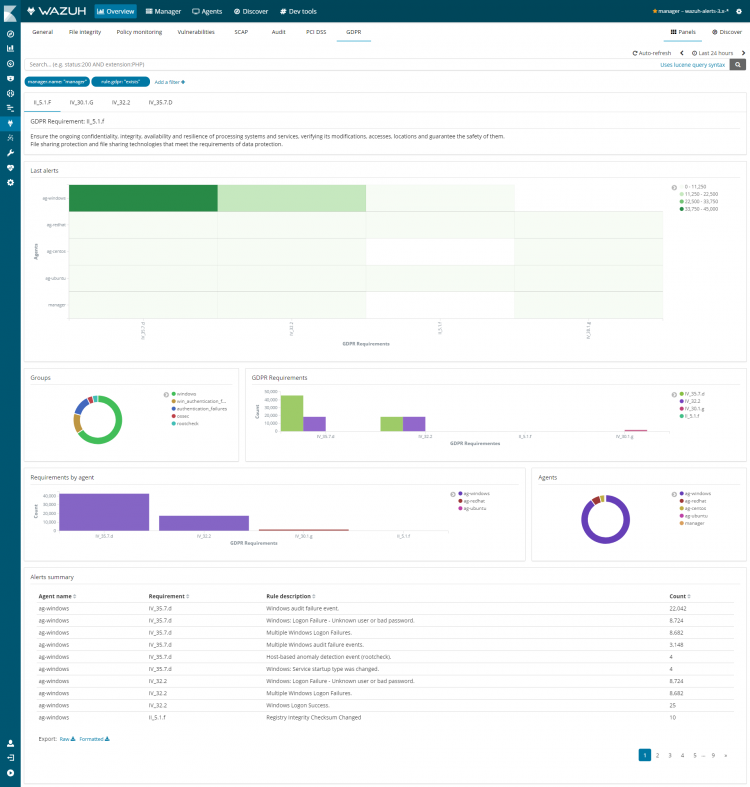
You can also check the Wazuh app dashboard specially built for GDPR:
We showed a use case where Wazuh helps to showcase GDPR compliance standards, but Wazuh can do much more: generation of all kinds of alerts, such as SSH or RDP brute force attacks, hidden processes detection such as rootkits, shellsock attack detection and reaction, malicious commands execution monitoring, suspicious network traffic capture with NIDS such as Suricata, scanning the system for malware, etc.
If you have any questions about this, don’t hesitate to check out our documentation to learn more about Wazuh or join our community where our team and contributors will help you.